23 Oct

Top Identity Threat Exposures You Need to Address Now
Cloud environment intrusions have increased by 75% year on year, and it takes around 120 days for organizations to detect cyberattacks in the cloud. Additionally, the rise of remote working has only intensified the complexity. With employees connecting from various
15 Oct

100 Breakthrough Prompts for Your Best User Access Review
User access reviews are vital for maintaining robust identity security and ensuring compliance across your cloud and SaaS environments. With the growing complexity of managing identities—both human and machine—security teams must continuously monitor and validate access to minimize risks like
01 Oct
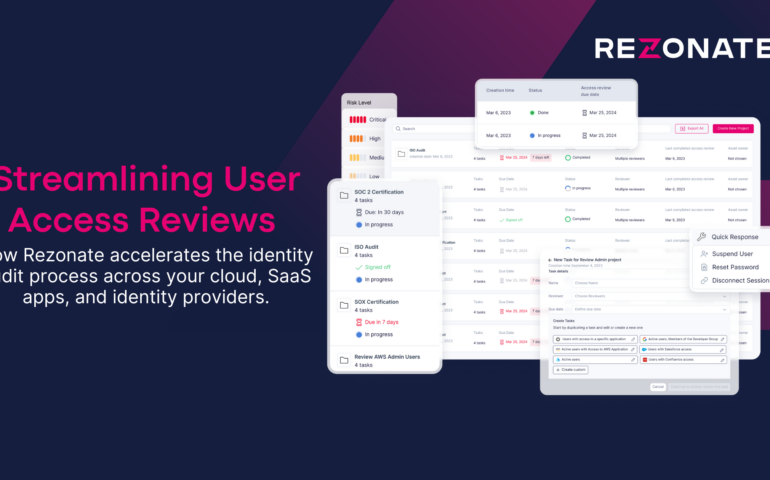
How to Unburden Your SaaS and Cloud Access Reviews
Managing access to cloud and SaaS applications is essential for securing critical business operations. Access reviews are a vital component of this process. They ensure employees have the appropriate permissions to do their jobs without exposing your organization to unnecessary
30 Sep
Your Pre-2025 User Access Review Plan: How to Ace Your Audits and Boost Security
This is your quick guide to conducting a water-tight user access review, passing your end-of-year IAM audits, and safeguarding your organization from identity threats before 2025 comes around. With the year drawing to a close, it’s the perfect time to
26 Feb

A Guide to the Gartner IAM Summit in London
Get a checklist for 6 critical learning objectives for the event, and jump start your agenda planning with our top 10 analyst session picks. In just one week, Europe’s version of Gartner’s IAM Summit will unfold in the vibrant city
15 Feb

How ITDR Could Have Helped Microsoft in the Midnight Blizzard Hack
Identity-based attacks are on the rise, but they can be prevented with the right identity threat detection and response (ITDR) measures. As winter crept in last year, so did identity threat actors. Microsoft revealed in January that the Russia-backed group

